Khatim Timestamp Server v2.0 Released
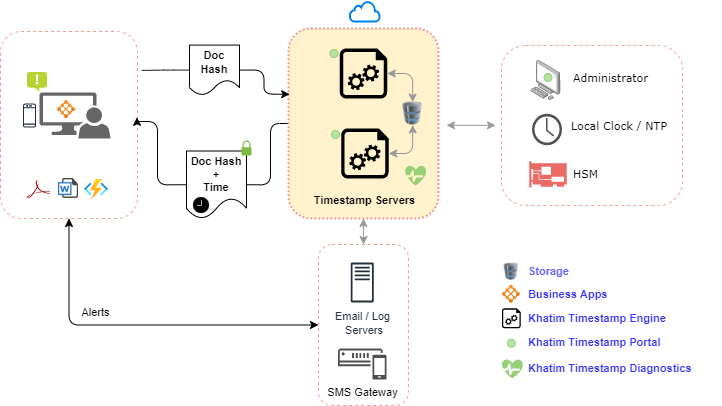
Finally Khatim Timestamp Server (KTS) v2.0 is released! The team at Codegic has worked hard to launch the next version of Khatim Timestamp Server (KTS). Version 1.0 focused primarily on the timestamping core while v2.0 focuses on usability. This release unveils the brand new GUI based interface for KTS. This interface is in addition to the the original command line interface where administrators can use console based commands to configure KTS, suited to headless environments. Now KTS admins can use either KTS console based client or GUI based interface to manage their timestamp servers. Here is a sneak preview of what is available in v2.0.
Dashboard
Charts based graphical statistics are a great tool to understand the health of your system and KTS dashboard provides that. The simple to use dashboard provides quick insight of critical statistics of your timestamp server be it running as a single instance or in a cluster. Admins can also filter the statistics shown on the dashboard using options Today, 7 days, 30 days, 365 days, This year, All or a custom date range.
PKI Admins can further see drilled down statistics to gauge the performance of their timestamp servers. Some quick explanation of these charts are:
Request
Breakdown of Successful or Failed timestamp requests.
Failures
Breakdown of failures mapped to the RFC 3161 i.e.
- badAlg: Unrecognized or unsupported Algorithm Identifier
- badRequest: Transaction not permitted or supported
- badDataFormat: Data submitted has the wrong format
- timeNotAvailable: TSA’s time source is not available
- unacceptedPolicy: Requested TSA policy is not supported by the TSA
- unacceptedExtension: Requested extension is not supported by the TSA
- addInfoNotAvailable: Additional information requested could not be understood or is not available
- systemFailure: Some unwanted error is found while processing the timestamp request
Alerts
Number of issues found in the KTS while generating the timestamp. These could be any of:
- NTP_COMM_FAILED
- TSA_SIGNING_FAILURE
- HSM_FAILED
- HSM_UP
- LICENSE_EXPIRED and more (see events below)
Policy
Breakdown of request based on the policy configured in the system.
Time source
Breakdown of the time source used for timestamp generation. Could be System Clock or NTP.
Hash Algorithm
Breakdown of hash algorithm (SHA2 etc.) used to generate timestamp.
Client IP
Breakdown of Client IP sending timestamp requests.
Host IP
Breakdown of Host IP receiving timestamp requests.
System
Provides a quick view of KTS server instances. In a load balanced environment multiple instances are shown. Guides admin when a KTS instance was:
- Provisioned
- By whom
- Host name & IP
Key Vault
Allows admin to:
- Configure PKCS#11 based HSMs or Smart Cards
- Generate cryptographic keys (RSA, ECDSA), CSR and Certificates for timestamping
- Import issued certificates back into the system
Certification Authorities
Allows KTS admins to view the default Certification Authorities which comes with the application. This is handy for quick testing of timestamp features without having to setup your own CA to issue timestamp digital certificates.
Timestamping
Timestamping feature is the core of KTS providing following sub features :
Policy
Admin can create multiple policies mapped to a policy OID, timestamp signing certificate, hash algorithm, time source and much more. This allows flexibility in meeting varying client needs.
NTP
Admin can setup NTP addresses which can be referenced in a policy as the authoritative time source for the incoming request.
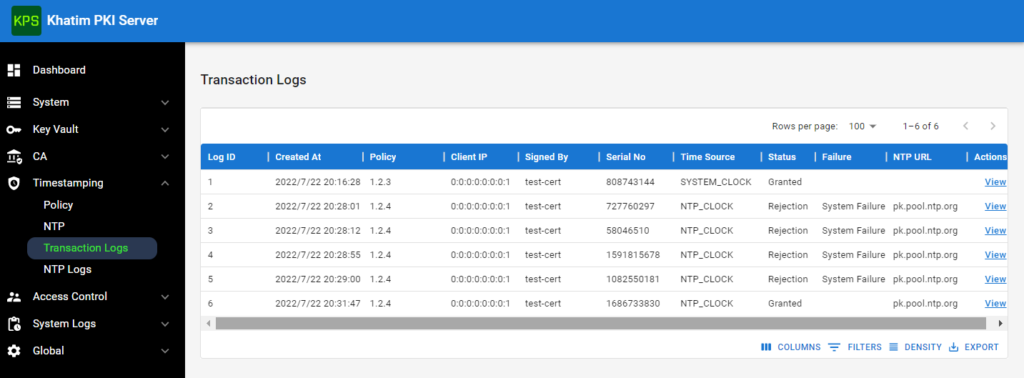
Transaction Logs
To help KTS admins identify the root cause of timestamp failures, KTS shows full list of timestamp transactions as they are created and more. Admin can see information like:
- Time when request is processed
- Incoming message imprint (data hash)
- Success or failure details
- Policy used to generate the timestamp response
- Detailed timestamp request/responses etc.
- IP address of requestor and host server
- Time source etc.
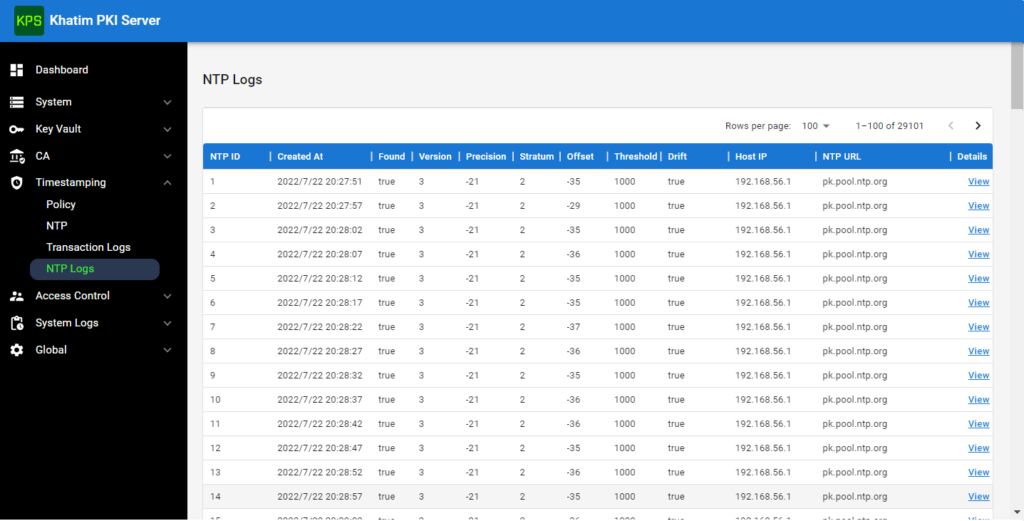
NTP Logs
The NTP logs provide precise information regarding what information was received from the NTP server. This is handy for auditing and compliance reasons. Admins can prove clients with NTP logs, what time they got from NTP server and whether it was trusted or not. Admin can also see:
- When the system clock drifted happened
- From which NTP server time was found
- To what extent the drift happened
Note that at KTS start, an NTP monitor is started which ensures system clock time is with in the range of the NTP time. This is done when at least a single policy is configured to use local system clock for NTP responses. In such a case, a call is made to the configured NTP servers to get the latest time. If the time found from the NTP server is beyond the system configured threshold to meet i.e. 1 second then it generates an alert for the administrator. In such an event, KTS will respond requests with timeNotAvailable response. If the policy is configured to use NTP server directly then for each timestamp request the registered NTP server is engaged to get trusted time.
Access Control
This features, allows admins to:
- Manage administrators
- View operator logs; admins can see full audit trial of the changes made by operators
System Logs
These logs are generated when ever there is any issue found during Timestamp processing to ensure critical components are performing as expected e.g. HSM, NTP etc. Some of these types of events are:
- NTP_COMM_FAILED
- TSA_SIGNING_FAILURE
- HSM_FAILED
- HSM_UP
- LICENSE_EXPIRED
- LICENSE_ABOUT_TO_EXPIRE
- OPERATOR_EXPIRY
- CERT_EXPIRY
- TSA_SIGNING_CERT_EXPIRED
- TSA_SIGNING_FAIL
- NTP_THRESHOLD
- NTP_COMM_FAILED_CRITICAL (when more than 50% fail)
- NTP_FAILED
These system logs are also emailed to the configured administrators as the event is generated and also incorporated in daily summary reports.
Summary
Well this was just a sneak preview of what KTS v2.0 has to offer. Codegic has planned further usability and functionality improvements for the next upcoming releases making it one of the secure, affordable and efficient Timestamping server. Further changes includes providing details time based graphs, better server management and more reporting so stay tuned!