Need for 'Digital Signature'
Although Digital Signatures have been around for couple of decades, due to the rise of computing machines but it has a decades old past. Signatures or identification marks have been used in history hundreds of years ago. Every era has used seals made from wooden, iron, ink to create unique, identifiable markings on paper or goods using either signet rings or wax. The core principle revolved around ‘being identified’. Hence the public at large could identify whether the king’s or state’s order or product is real or from imposter. Later signatures using colored ink came which somewhat complemented seals. Signatures became more common as they were handy i.e. no need to carry the seal everywhere you go.
Originally seals or signatures were more of kings or state’s needs. Later on, the need to identify involved masses. As the need arises, the public at large also had to be identified.
The identification of masses initially started with thumb impressions. Later with the pen getting widely used, hand signatures gained traction. Starting the 19th century, hand signatures using quill and then later pen became popular till the wide use of computers hence a mere hand signature on paper became Digital Signatures.

Paperless Office
With deforestation and depleting sources of wood catalyzed the switch to other environment friendly options. As computers become common in businesses hence the wide use of digital documents replacing their paper counterparts. Other equipment like fax machines became common as they helped sending paper from one part of the world to another. As the internet shook the world, their usage soon faded away as well.
Now a paper-less office is no more a dream. With application and services accessible over the internet along with power computing machines and document formats like PDF, documents can be viewed, edited, processed any time and any where. With millions of documents created every month, their integrity and authenticity became important. Business documents and communications can’t survive without trust hence rose the need of Digital Signatures.

What is a Digital Signature?
Digital Signature is hence just a counter part of hand signature in the electronic world. A squiggle mark on a paper is replaced with a digital mark which traces back to the one who created it. It further adds the security feature of forgery or tamper detection and Non-repudiation. It all boils down to mathematical numbers created on a particular algorithm.
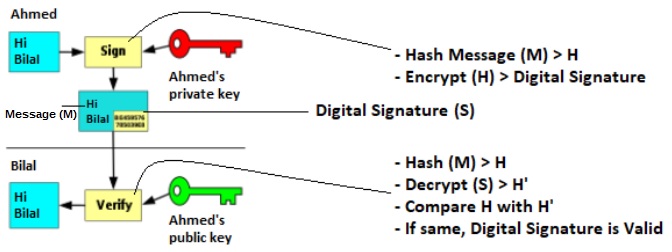
To explain the concept in simple terms, person Ahmed is assigned two unique numbers K and P, only known to him. He wants to send a message to Bilal. He then uses K using a particular calculation / algorithm to create another number say S (Digital Signature). He can then send his message M along with S to Bilal. Bilal can now use P to verify M. In case any of M or S is changed, Bilal will not be able to verify.
In the above, Message (M) can be replaced with any content be it your emails, word documents, images, media etc. Going further M can be transactions in xml, json, code, executables etc. Good thing about K and P is that they are related i.e. any thing encrypted with K can be verified with P and vice versa. K is called a private key hence to be kept privately and P a public key hence to be given to signature verifiers. These are also called as asymmetric keys as P and K are different.
Digital signatures are normally done using the two most popular algorithms RSA and ECDSA. RSA being old is still in wide use while EDCSA being faster is gaining popularity among devices e.g. IOT, smartphone etc. These algorithms are responsible for creating the key pairs i.e. K and P and also for the encryption and decryption. Digital Signatures both rely on cryptography and specifically public key cryptography.
Security in Digital Signatures
Security through obscurity is now a thing of the past. One can’t just hide the algorithm for too long. Kerckhoffs’s principle is commonly used in any crypto system where security strength lies in the key (its strength & secure storage) and not the algorithm. Both RSA and ECSA rely on generating unique K and P keys and hence their strength and protection defines how strong the security is. Security in digital signature hence relies on the security of these keys, specifically the K part. If K is known to the unwanted, your security is gone. K is hence kept safely with (at minimum) password protection on computers, USB tokens, HSMs while P is given out publicly to recipients so that they can verify the digital signatures. In summary security of digital signature relies on these factors:
- How good the digital signature algorithm is
- How good the key (K) strength is
- How good the hashing algorithm is
- How good the protection of K is
How good the digital signature algorithm is in general
In terms of algorithms RSA and ECDSA both are good enough. So far there is no known weakness identified in their two algorithms. They don’t have any flaws which could result in a similar outcome as in the case of the Enigma crypto machine.
Digital signature strength lies in the key!
K (Private Key) is just another random number. Any one guessing that means any one can send a message on your behalf or change your message during transit and sign it again to hide tampering.
On key sizes, especially talking about RSA, comes in variety from 100 to 8192 and beyond. On December 12, 2009 RSA-768 was cracked in 2 years by a group of mathematicians. A decade ago an RSA key of 512 (1×10154 permutations), 1024 (1×10308 permutations) was termed as sufficiently strong. As of 2020, 1024 bit key pairs are considered to be weak and not recommended. As computing power is increasing every year and super computers are being built, threats of cracking big numbers are increasing. NIST now recommended to use RSA 2048 bit keys size which will be strong enough till 2030 and beyond 2030 recommends use RSA 3072 bit keys. Similar recommendations are there for Symmetric encryption key sizes i.e. 3DES till 2022 and then disallowed from 2023 and recommend AES 128 till 2030 and AES 192/256 for 2030 and beyond.
Same goes with ECDSA based keys where a key size ranging 160 to 223 is deprecated and recommends minimum 224 or more till 2030 and then 384 or more for 2030 and beyond.

What about Hashing?
In layman terms, hashing is just reducing the size of the input. If you have 10 GB sized data, you can’t just encrypt it with a RSA 2048 bit key as it will take ages! Hashes is one way; means you can’t identify the original document from its Hash. Using a weak hashing strength will do no good even if you use RSA 2048 bit key size or more.
Some of the popular hashing algorithms are MD5, SHA-1, SHA-2 and now SHA-3. MD5 is long gone and not recommended although still used in some legacy products. SHA-1 produces a hash of 160 bit which is now subject to collision attack. This means you can get a collision if you generate 2160+1 unique message. SHA-1 (160 bit) was cracked a few years back and hence not recommended by NIST. What’s left is SHA-2 and its future not so common one, SHA-3. NIST now recommends to use SHA-2 (224+) till 2030. Post 2030 one must use SHA-256, SHA-512 or SHA-3.
Here is a list of hash of text: This is Codegic
- MD-5
1c2b6846d9e66b98aafb94566974a42e - SHA-1
2cc69dc75e9fb87bcb49c8af16d6db6cf1cf57a3 - SHA-256
b8174abcb3af36737167d34438eaafff4bdfeac40e665db6e04c569085e61140 - SHA-384
- 05e427af3e41436e7821633f5f9d155b5573e30092a310cbcd76555ef0aa5a397a24ea73427889bcae7820a4f0b3e447
- SHA-512
13302abb1dec529526a12652fc1d89c24cb66955c625bdd92ae84791ce8e96440ed6867cc61c1352e8fbb8df7062fedb7075b69eaaaa5d29aa9cfb21814dd14d

NIST Recommendations
NIST recommendation on the use of Hashing and Asymmetric key algorithms
Deprecated Algos
- RSA 512, 1024
- ECDSA 160, 223
- MD5, SHA-1
Safe to use Algos before 2030
- RSA 2048 and more
- ECDSA 224 and more
- SHA-2 (224 and more)
Safe to use Algos beyond 2030
- RSA 3072
- ECDSA 384 and more
- SHA-2 (256 and more), SHA-3
See Reference

Protect your Keys!
As goes the saying, your security is as strong as the weakest link, how good the security be if you don’t safeguard your keys. It is more easier for hackers to get inside your computer, phone to steal your unprotected keys then to crack it using brute force attack. Some of the common ways of storing keys are:
- No security – Store in plain
- Low level security – Storing on your computer or device with password protection
- Medium level security – Storing inside USB token or smart card (again password protected)
- Highest level security – Storing inside Hardware Secure Modules (HSM)
You may keep your keys as plain text for just testing, exploring their structure although again it is a bad practice!

Password protected keys
Most oftenly these are stored as PKCS12/PFX files protected with a password. Ensure the password must be strong enough to avoid brute force attack. You may use this protection method for keys used to login to test or production systems or signing documents. All the popular operating systems i.e. Microsoft, Linux and MAC support them.
USB tokens or Smart Cards
These are small, hardware devices also called security tokens specifically designed to protect user’s private keys. These allow keys to be generated inside the embedded cryptographic chip inside and remain there throughout their lifetime. Some may disable the USB token or Smart Card if an incorrect password is used a number of times. These can be reused if locked after admin intervention. As these are for individual’s usage hence have low disk space allowing not more than few private keys. You may buy a token for less than $30. USB tokens are used to create digital signatures for desktop environments.

Hardware Secure Modules (HSM)
HSMs are similar like USB tokens but have a bigger form factor. Again these are specialized purpose built, security focused machines keeping your business sensitive keys. Depending upon their storage space, they may keep millions of keys. They have more advanced security controls as compared to a USB token. They have hardened OS and are certified against FIPs 140-2 standards. An HSM can detect an intrusion and hence may wipe the entire data inside (make sure you keep a backup before this happens!). As per webtrust a publicly known Certification Authorities must store their private keys in an HSM. Some secure deployments require a common criteria certified HSM as well.
HSMs are expensive and could be around a few thousand dollars. They come in both network or PCI based. A somewhat non-exhaustive list of HSM can be found here. For a medium sized usage, a cheaper alternative (under $999) is from Yubico named YubiHSM. There have been reports of even HSM hacked. Having said there is no such thing as 100% secure or fool proof security. Having security in place is far better than having none!

Cloud based HSM
HSMs are generally expensive and adding few of them covering staging, replication cost a fortune hence only big corporations, governments, defence departments with deep pockets can afford it. As there was a need for small and medium sized companies to store their secret info and keys hence came the Cloud to the rescue. Some of the notable cloud based HSM providers at Azure Key Vault, Amazon HSM and Google Cloud KM. All of these cloud offerings have their strengths and pricing. A quick comparison might help you pick the right one for your needs.

Support for Digital Signature in Applications
As long as the software supports, you can digitally sign any data with your PKCS#12 files or USB tokens. Common applications which let you digitally sign data are:
- Document processing software (Microsoft Word, Libre Office, Open Office, Outlook)
- PDF processing software e.g. Adobe Reader, Foxit, NitroPDF, PDF Sign&Seal etc.
- Custom XML processing software
- Executable, Installer signing software (SignTool)

Digital Signature Formats
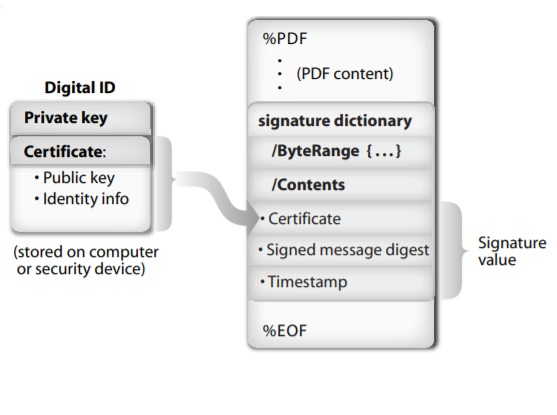
In a nutshell digital signature is encrypting a hash with a key (private key) but based on the type of data it signs, different formats have to be devised. This has led into different standard bodies like ISO, IETF and OASIS to come up with rules of creating digital signatures and how they can be embedded inside original documents for transportation. This standardization also helped in compatibility among different operating systems and tools. Some of the digital signature standards are:
As the need to keep digital signatures for long term storage arised, so did new standards were formulated hence the CAdES, PAdES (Part 1, Part 2, Part 3, Part 4, Part 5, Part 6) and XAdES standards.
Digital Signature Future
Doing business electronically is here to stay as it’s fast, efficient and cheap. Financial institutions, Governments, Defense are now adopting paperless ways of doing business. Some example use cases are:
- Government wants public to apply for Identity cards, passports where ever they are
- Financial institution want clients to apply for account and sign documents with ease
- Businesses want interoffice discussion to be secure and also traceable with their identities
As more business is done electronically the demand of integrity and identity is growing and similarly the threats. One can sit in one part of the world and disrupt businesses across the globe. This has led to businesses relying on the time and tested science of cryptography and especially public key cryptography and PKI.
Governments across the world are now adopting e-signatures (a term used commonly for digital signature although differs technically). Terms such as eSignature, eTimestamp and eSeal are formulated to secure businesses across international boundaries. To enforce these standard some legislations is also being done:
- USA: E-Sign Act and more state laws
- European (EIDAS):
PKI is here to stay and is evolving every year. For a glimpse into the future, quantum cryptography is yet another upcoming domain where researchers are continuously working to ensure new uncrackable ways of digital signature are found. NIST has already started working on identifying post quantum algorithms so sit tight.

