Security Solutions
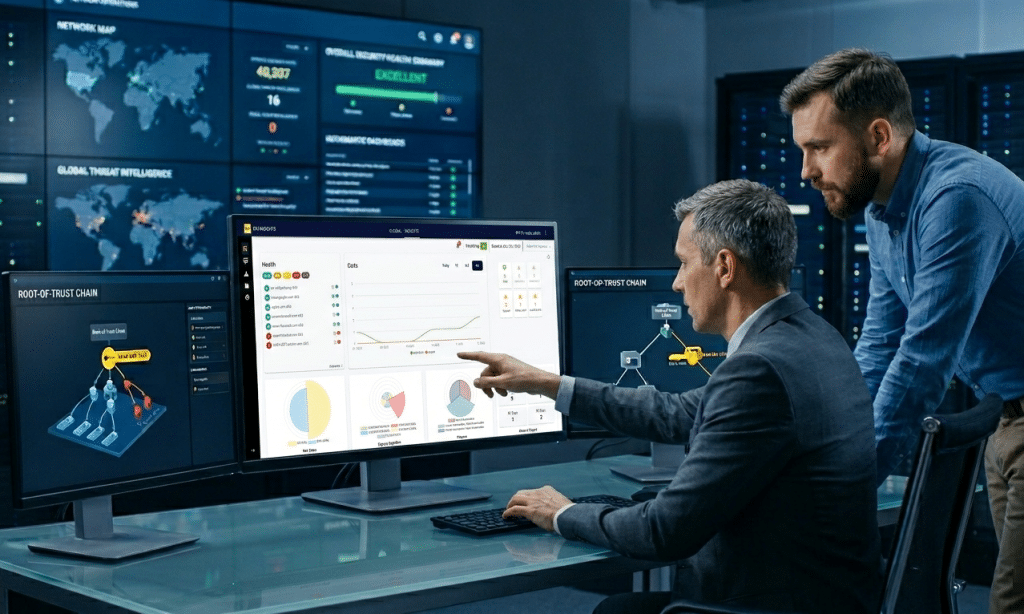
From identity to integrity, Codegic delivers scalable trust infrastructure for your business.
Khatim PKI Server
Powerful & Scalable Certification Authority / PKI server. Empowering trust, for a secure tomorrow
Khatim Sign Server
ETSI, EIDAS compliant, digital signature server bringing integrity + trust in your enterprise for bulk processing
Khatim TSA Server
High assurance cryptographic, trusted timestamp server with market-leading performance
KhatimDoc
High Trust, Flexible, Contract Signing. Boost Collaboration, Workflows, Privacy & Accelerate Signatures
Khatim OCSP Server
High Assurance, Resilient, OCSP server with industry-leading speed
Khatim RA Server
Self Service, Scalable RA server for complete Certificate Lifecycle management (CLM)
Words from Client
Leading companies rely on us for their PKI and digital signature needs
We were struggling with our PKI implementation when Codegic came to the rescue. They not only sorted our technical issues but also designed the whole PKI for the infrastructure.
Hemal Patel, CEO, Ray Pte. Ltd.
Security Services
Grow your business with world class security services
AATL powered PDF Signing
Convert your untrusted PDF documents into trusted ones with the power of the Adobe Acrobat Approved Trust List (AATL).
PKI Development
Enhance your business with PKI solutions that prioritize Digital Trust including CAs, Digital certificates, Digital Signatures, Timestamping, PKI Monitoring and more.
Get X.509 Digital Certificates
Easily test, issue, and validate X.509 digital certificates to simplify adoption, evaluate trust models and accelerate secure deployments.
See PQC into action!
Quantum threats demand early PQC adoption as classical security erodes. Learn & play with Post Quantum Crptography to protect long-lived certificates and digital trust.
Memberships
Always innovating, actively engaged. Stay ahead of the curve with our PKI solutions.






Latest blog posts
Read more about our latest news posts and be informed
Let’s Get in Touch
Give us a call or drop by anytime, we endeavor to answer all inquiries within 24 hours on business days.