What eIDAS PKI compliance means
eIDAS (EU Regulation on electronic identification and trust services) defines the rules and certificate profiles required for Qualified Trust Service Providers (QTSPs) and for issuing Qualified Electronic Signatures (QES). Compliance isn’t just about cryptography – it’s about operational controls, evidence, and producing certificates that will be accepted across EU member states for legal and regulatory use.
Khatim PKI Server is designed to help organizations and QTSPs meet those technical and operational requirements: it handles the certificate formats, extensions, validation data, key protection and auditable processes that regulatory assessors expect.
"Qualified assurance you can prove"
eIDAS features & certificate extensions supported
Khatim PKI Server exposes a templates-based certificate authoring model that makes it straightforward to produce eIDAS-compatible certificates. The Templates section of the Administration Guide documents the complete set of extensions you can configure. In practice, It supports the commonly required eIDAS/ETSI extensions and controls used by QTSPs, including (but not limited to):
-
certificatePolicies – attach policy OIDs required for qualified profiles.
-
qcStatements / QCType / QCCompliance – embed ETSI qualified-certificate statements (QES indicators and qualifiers).
-
keyUsage and extendedKeyUsage – restrict certificates to allowed uses (signing, non-repudiation, TLS, etc.).
-
subjectAltName and other subject attributes required by policy.
-
authorityInfoAccess (AIA) and CRL Distribution Points (CDP) – enable verifiers to locate validation data.
-
OCSP responder configuration – for live OCSP checks and issuing of OCSP responses for compliance.
-
-
Custom/enterprise OIDs and Microsoft-specific CSR extensions – It supports vendor or environment-specific extension OIDs when needed (e.g., Microsoft enrollment extensions) so you can meet platform-specific requirements.
For the full OID list and template options see the Templates section in the Khatim PKI Server Administration Guide.
It’s template editor lets PKI administrators create, version and enforce these extension sets so every qualified certificate issued conforms to the selected eIDAS profile.
"Everything a qualified certificate needs - defined in a template"
PSD2 & payment-specific support
PSD2 imposes specific technical and operational needs for financial services (e.g., secure signing of API interactions, transaction validation and strong customer authentication). It’s PSD2 guidance and feature set (see the PSD2 support page) maps to those needs by:
-
Enabling certificate templates and policies tailored for PSD2 use cases.
-
Ensuring appropriate EKUs and policy OIDs are present for payment-related certificates.
-
Providing strict key custody via HSMs and segregated Key Vaults to meet financial audit expectations.
-
Supporting automated revocation/OCSP flows so gateways and verifiers can quickly check certificate status.
-
Producing traceable logs and reports that help demonstrate PSD2 operational controls.
If you are operating in payment environments, it makes it straightforward to produce the certificate artifacts and evidence PSD2 auditors expect.
"Payment regulation aligned - certificates that work for PSD2 flows"
Implementing and proving compliance
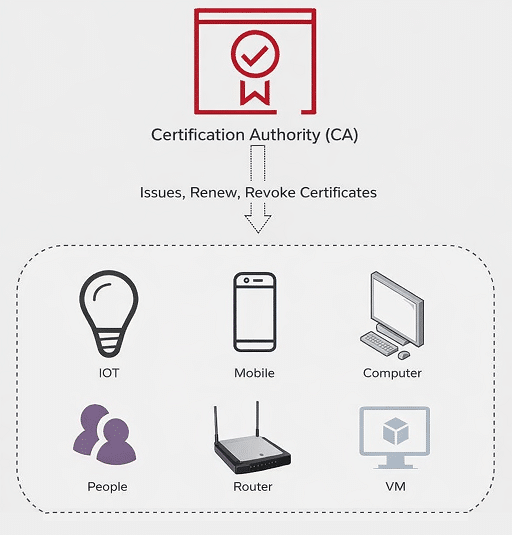
Khatim PKI Server combines technical capability with operational controls to simplify eIDAS readiness:
-
Template-driven authoring: create eIDAS/QES certificate profiles once and enforce them across issuance points.
-
HSM-backed key custody: generate keys in hardware or map keys to cloud KMS; keys never leave trusted boundaries.
-
Qualified signature workflows: built-in support for timestamping, required QC statements and long-term validation (LTV) plumbing.
-
Audit trails & logging: every issuance, renewal, revocation and policy change is recorded for forensic and conformity assessment.
-
OCSP/CRL & validation: dynamic revocation provisioning and configurable responders to meet verifier expectations.
-
Reporting & evidence packs: automated daily summaries, signed log exports and compliance reports for assessors and auditors.
-
Flexibility for platform specifics: support for Microsoft-specific extensions, PSD2 profiles, and other vendor-specific OIDs where required.
These features let QTSPs and enterprise PKI teams both implement compliant issuance and demonstrate it – an essential requirement for certification and public trust.
"Policy, protection, proof - delivered together"
Getting started: best practices for eIDAS deployment
-
Choose or define the policy OIDs you must issue under (qualified, advanced, PSD2, sector-specific).
-
Author templates for each certificate profile (include QCStatements, certificatePolicies, EKUs, AIA/CDP entries).
-
Protect keys by generating or importing them into HSM Key Vaults, and map CA roles to segregated slots.
-
Enable timestamping and LTV options for long-lived signatures where required.
-
Configure revocation responders (OCSP/CRL) and test verifier flows.
-
Test PSD2 and other sector scenarios with sandbox clients and perform pre-assessment checks.
"Plan, enforce and prove"
Words from Client
Leading companies rely on us for their PKI and digital signature needs
We were struggling with our PKI implementation when Codegic came to the rescue. They not only sorted our technical issues but also designed the whole PKI for the infrastructure.
Hemal Patel, CEO, Ray Pte. Ltd.
